Most modern technology carries some element of risk which is usually carefully managed and controlled by security measures. But there’s always someone looking to exploit these risks further. Updates and security patching is therefore constantly being released to plug emerging vulnerabilities.
The challenge for most organisations is how to stay on top of their patch management.
The Challenge Of Security Patching
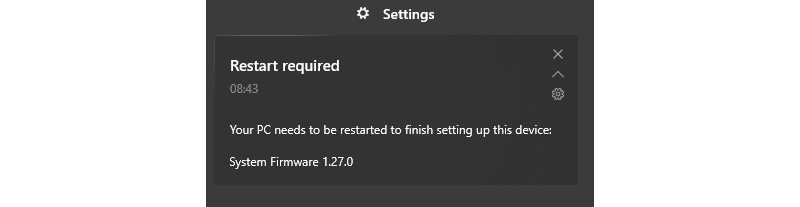
Patching is not necessarily straightforward. There are factors that need to be taken into account when applying a patch:
- It can be time-consuming as key patches may need testing before roll-out. By testing, any problems are easily identified and resolved. However, this can be time and resource-heavy.
- You can only apply a patch to something that you know you have. Keeping an accurate record of all applications and hardware across an organisation is crucial to maintaining a healthy IT environment.
- Security patching contains an element of risk. There is the possibility that applying a patch could create an unforeseen issue elsewhere, which is why it is so important to keep accurate records of existing applications and logs of changes.
- A failed patch roll-out has an impact on every business no matter how big or small it is. It can bring a business to a grinding halt and stop employees from doing their job. It can also increase the risk of a cyber-attack.
- Some applications or hardware may also require third-party involvement if it’s leased.
It’s not all negatives however: patching can also deliver new features, increase performance and improve user experience. But it is a continuous housekeeping exercise.
This, therefore, reiterates the importance of a planned approach to patching.
The Value Of Patch Management
It pays to plan your approach to patching. Organisations are usually time-poor, but security is critical. Having a professional partner take care of patch management can therefore be of benefit in minimising business risk.
Security patching is an activity given priority during as part of Akita’s Proactive General Maintenance – whether conducted onsite or remotely. This ensures our customers’ workstations and servers are fully protected.
Other essential IT activities undertaken as part of Proactive General Maintenance include:
- Backup verification – Restoring a test set of files from an organisation’s backups to check that their backup is working effectively and has not suffered any corruption.
- Asset management – Reviewing what is in place and why it is used in order to manage operational risks (notably GDPR).
- Antivirus review – Checking the threats an organisation has faced and adjusting scans and software accordingly.
To discuss security patching and Proactive General Maintenance for your organisation, please get in touch:





