Whether developing SaaS platforms, enterprise applications, or specialist industry tools, software organisations manage valuable intellectual property, sensitive customer data, and highly connected digital infrastructure. And this makes them one of the most targeted for cyber attacks.
The challenge is particularly complex: with development environments, cloud platforms, APIs, and customer-facing systems, software companies face multiple attack surfaces that threat actors actively exploit.
Building cyber security for software businesses, therefore, requires more than basic protection. It demands a structured strategy covering infrastructure, development practices, identity security, and ongoing monitoring.
The Challenge Of Cyber Security For Software Companies
Software companies operate in fast-moving environments. Development teams frequently work across distributed environments using cloud platforms, remote access tools, and collaborative development pipelines. While this accelerates product delivery, it also expands the potential entry points for attackers.
Infrastructure outages or security incidents can have immediate consequences. Even minor disruptions can delay development cycles, disrupt deployments, and affect customer satisfaction or investor relations.
Reliable IT infrastructure and strong cyber security controls are therefore essential to maintaining productivity and uptime.
In addition, modern software businesses increasingly deliver cloud-based services. This means they are responsible not only for protecting internal systems but also for safeguarding their customers’ data and operations.
Secure Software Development Practices
One of the most important foundations of cyber security for software businesses lies in secure development practices.
Security must be embedded into the development lifecycle rather than added after products are built.
The UK government’s Software Security Code of Practice highlights the need for organisations that develop or distribute software to implement consistent security and resilience measures throughout development and maintenance processes.
Essential practices include:
- Secure coding standards to prevent vulnerabilities such as injection attacks
- Regular code reviews and automated security testing
- Vulnerability scanning within development pipelines
- Patch management to quickly remediate security issues
Adopting a “secure by design” approach ensures that applications are resilient from the outset.
For software businesses, this is particularly important as vulnerabilities within applications can expose thousands of customers simultaneously.
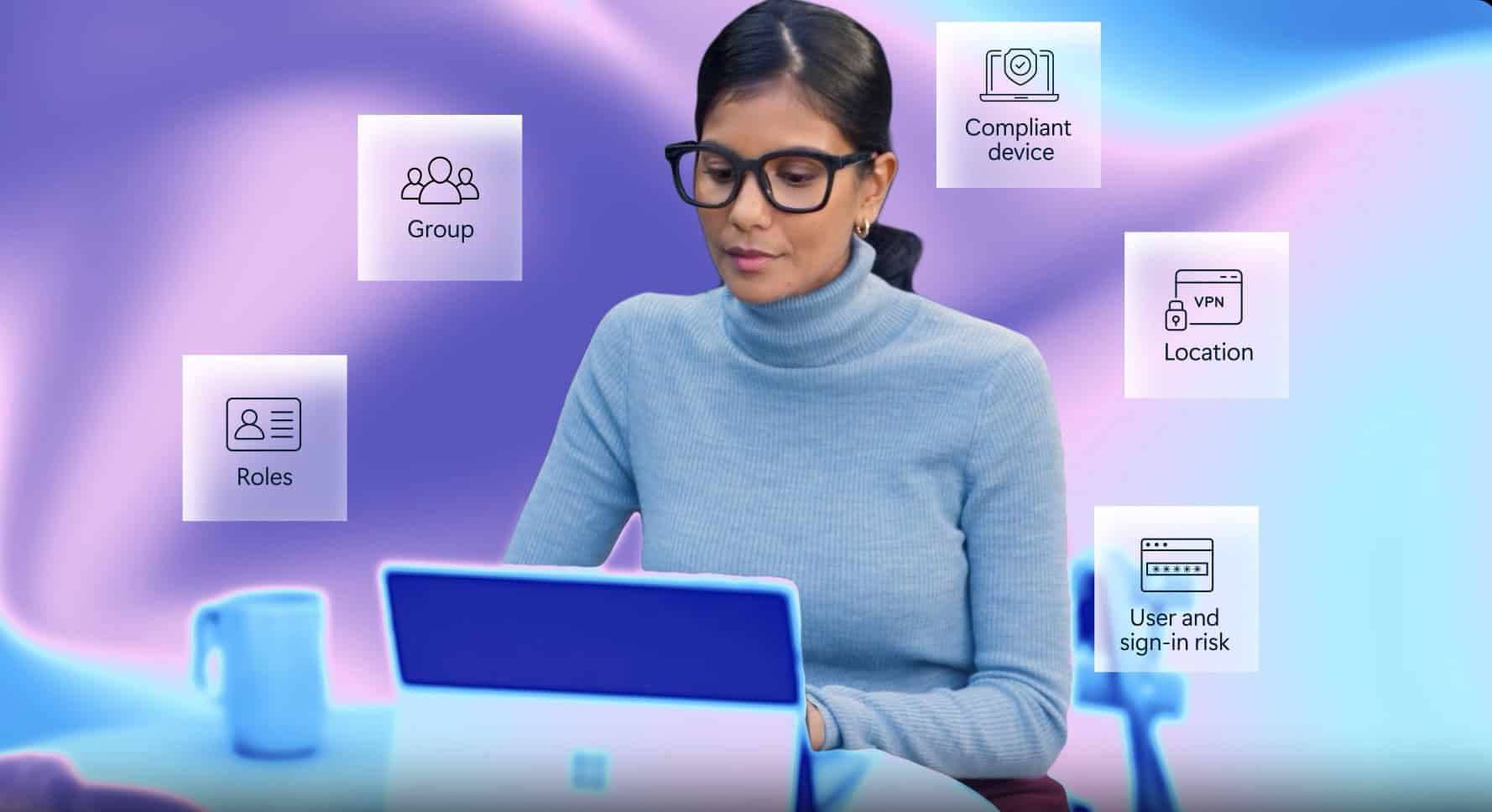
Identity and Access Management
Identity is one of the most common attack vectors for cyber criminals. Compromised credentials can allow attackers to access development environments, production infrastructure, and customer data.
Effective identity management requires strict control over who can access systems and what permissions they hold. This includes implementing:
- Multi-factor authentication (MFA)
- Role-based access controls
- Privileged access monitoring
‘Privileged Access Management’ solutions play a key role in protecting administrative accounts that provide extensive system access. By controlling and monitoring privileged users, organisations significantly reduce the risk of unauthorised access or insider threats.
Adopting a least-privilege approach ensures employees only have access to the systems and data required for their role.
Securing Cloud and SaaS Environments
Many software companies operate entirely within cloud environments, delivering services through SaaS platforms. While cloud infrastructure provides scalability and agility, it also introduces new security challenges.
Cloud applications must be carefully configured and continuously reviewed to reduce the risk of common cyber attacks. Secure configuration, access controls, and ongoing monitoring are critical to preventing breaches in SaaS environments.
Some of the most common SaaS security risks include:
- Misconfigured access permissions
- Weak identity controls
- Insecure APIs
- Insider threats
- Data leakage from third-party integrations
Because SaaS platforms often host large volumes of customer data, breaches can have severe reputational and legal consequences. A strong SaaS security posture protects both the provider and its clients while improving trust in the platform.
Continuous Monitoring And Threat Detection
Cyber threats evolve rapidly, which means prevention alone is not enough. Software businesses must also focus on detection and response.
Continuous monitoring allows organisations to identify suspicious activity before it escalates into a serious incident. This includes monitoring:
- User behaviour and login patterns
- Network activity
- System logs
- Cloud environments
- Development pipelines
Continuous exposure management approaches are increasingly used to identify vulnerabilities and misconfigurations across an organisation’s entire digital ecosystem. These systems provide real-time monitoring and prioritise risks so security teams can remediate them quickly.
For many organisations, partnering with security specialists or managed security providers enables access to 24/7 monitoring and rapid incident response capabilities.
Data Protection And Compliance
Software businesses frequently process personal data, financial information, and commercially sensitive client records. Protecting this data is both a security requirement and a legal obligation.
In the UK, frameworks such as Cyber Essentials provide a baseline set of security controls designed to protect organisations from common cyber threats.
Certification demonstrates that a business has implemented essential protections such as secure configuration, access controls, and patch management.
Beyond compliance, strong data protection builds trust with customers and partners. Organisations that demonstrate mature cyber security practices are more likely to win contracts, particularly with enterprise clients or regulated industries.
Managing Third-Party and Supply Chain Risk
Software companies rarely operate in isolation. Modern applications often rely on third-party libraries, cloud providers, integrations, and external development tools. Each additional dependency introduces potential security risk.
Supply chain attacks have become increasingly common, exploiting vulnerabilities in widely used software components to compromise multiple organisations simultaneously.
To reduce these risks, software businesses should:
- Assess the security practices of vendors and partners
- Monitor third-party software components
- Maintain an up-to-date software bill of materials (SBOM)
- Apply patches and updates promptly
Managing third-party risk is now a critical part of cyber security strategy, particularly for SaaS providers whose platforms integrate with many external systems.
Building a Cyber Security Culture
Technology alone cannot protect an organisation. People and processes play an equally important role in maintaining strong cyber security. Afterall, over 90% of cybersecurity breaches are caused by human error.
Developers, engineers, and operational teams should receive regular security training that helps them identify threats such as phishing attacks, credential theft, and social engineering.
Security awareness programmes also encourage teams to adopt best practices when handling data, managing credentials, or deploying new systems.
When cyber security becomes part of company culture rather than a separate technical function, organisations build resilience across every layer of the business.
Strengthening Cyber Security Through Strategic IT Support
For many software companies, maintaining enterprise-grade security internally can be challenging. Development teams are often focused on building products rather than managing infrastructure security.
Specialist IT providers can help bridge this gap by delivering services such as infrastructure management, threat monitoring, and security strategy development. With the right support, software businesses can maintain secure and reliable IT environments while allowing internal teams to concentrate on product innovation.
Ultimately, cyber security is not just about preventing attacks. It is about protecting intellectual property, maintaining operational continuity, and enabling businesses to scale securely.
As the software industry continues to expand, organisations that embed strong cyber security practices into their operations will be best positioned to innovate, grow, and maintain customer trust.
Discover more about how Akita support software developers and businesses:
More