Identity and Access Management (IAM) sits at the centre of modern cyber security strategy. As organisations adopt cloud platforms, mobile working, and integrated business applications, controlling who can access systems and data has become increasingly complex.
IAM provides the framework that allows organisations to manage digital identities and regulate access to critical resources in a secure, structured way.
For businesses operating across multiple platforms and services, IAM is not simply a security tool. It is a governance framework that protects sensitive information, ensures regulatory compliance, and enables employees to work productively without unnecessary access barriers.
What Is Identity And Access Management?
Identity and Access Management refers to the policies, technologies, and processes used to manage digital identities and control user access to systems, applications, and data within an organisation.
At its core, IAM answers three fundamental security questions:
- Who is the user?
- What are they allowed to access?
- How is that access verified and monitored?
An identity typically represents an individual user, but it can also refer to applications, services, or devices that require access to organisational systems. IAM solutions manage these identities throughout their lifecycle, from initial account creation through to modification, monitoring, and eventual deactivation.
Access management governs the permissions attached to those identities. This determines what resources users can interact with and under what conditions. For example, a finance employee may require access to accounting software but not to engineering systems, while a contractor may only have temporary access to a specific project environment.
Modern IAM platforms often incorporate several key components:
Authentication: Verifying that a user is who they claim to be, typically through passwords, biometrics, or multi-factor authentication.
Authorisation: Determining what resources the user can access once authenticated.
Identity lifecycle management: Managing user accounts as employees join, change roles, or leave the organisation.
Access governance: Providing oversight and auditing to ensure access privileges remain appropriate.
Single sign-on (SSO): Allowing users to access multiple systems using a single authenticated identity.
In a cloud-first business environment where employees regularly interact with dozens of applications and services, IAM ensures access remains both secure and manageable.
Why Identity And Access Management Is So Important
IAM has become a critical element of organisational security because identity is now one of the most common attack surfaces targeted by cyber criminals. Compromised credentials remain a leading cause of security breaches, making strong identity controls essential for risk reduction.
A well-implemented IAM strategy delivers several important business benefits.
Strengthening Cyber Security
By enforcing strong authentication methods such as multi-factor authentication and conditional access policies, IAM significantly reduces the likelihood of unauthorised access. Even if login credentials are compromised, additional verification steps help prevent attackers from gaining entry to systems.
Supporting The Principle Of Least Privilege
IAM allows organisations to enforce least-privilege access policies, meaning users only receive the permissions required to perform their job roles. This limits the potential damage if an account is compromised and reduces the risk of accidental data exposure.
Improving Compliance And Audit Readiness
Many regulatory frameworks require organisations to demonstrate control over who can access sensitive data. IAM platforms provide centralised reporting and auditing capabilities that help businesses prove compliance with standards such as ISO 27001, GDPR, and industry-specific regulations.
Enhancing User Productivity
Without effective IAM, employees often struggle with multiple logins and access delays. Features such as single sign-on streamline access to applications, allowing users to authenticate once and work across multiple platforms without repeated logins.
Supporting Hybrid And Remote Working
Modern workforces operate across office environments, remote locations, and mobile devices. IAM ensures secure access regardless of location, device, or network, enabling organisations to maintain productivity while protecting critical resources.
Reducing IT Administration Overhead
Manual account management is time-consuming and prone to error. IAM systems automate tasks such as user provisioning, access requests, and role changes, reducing the workload for IT teams while improving security consistency.
How Microsoft Security Supports Identity And Access Management
Microsoft has invested heavily in identity-centric security as part of its broader cyber security ecosystem. Its cloud-based identity platform provides organisations with the tools needed to manage access securely across Microsoft services and third-party applications.
The cornerstone of Microsoft’s IAM capabilities is Microsoft Entra ID (formerly Azure Active Directory). This platform acts as the central identity provider for organisations using Microsoft cloud services and integrates with thousands of third-party applications.
Microsoft Entra ID enables organisations to manage user identities, authenticate access, and enforce security policies across applications, networks, and devices. It supports single sign-on across cloud and on-premise systems, allowing employees to use one identity to access services such as Microsoft 365, Dynamics 365, and external SaaS applications.
One of its most important capabilities is multi-factor authentication (MFA). By requiring an additional verification step beyond a password, such as a mobile notification or biometric confirmation, MFA dramatically reduces the risk of compromised accounts.
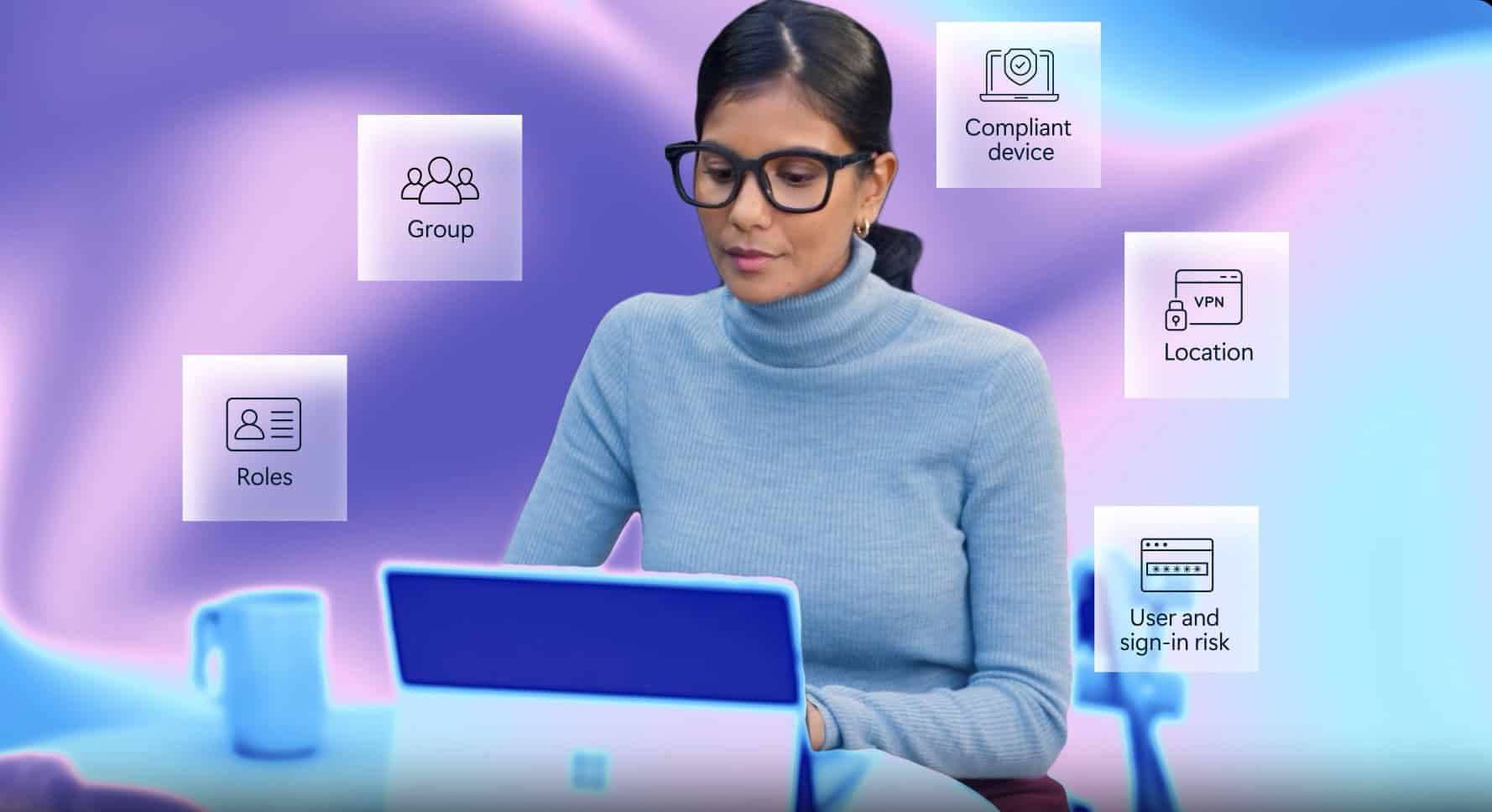
Microsoft also provides conditional access policies that evaluate risk signals before granting access. These policies can assess factors such as device security status, user location, sign-in behaviour, and application sensitivity. If a login attempt appears risky, the system can require additional authentication or block access entirely.
Privileged Identity Management (PIM) adds another layer of control for administrative accounts. Rather than granting permanent elevated privileges, PIM allows organisations to provide just-in-time access to critical systems. This ensures that administrative privileges are active only when required, reducing the attack surface associated with privileged accounts.
Microsoft Defender for Identity complements these capabilities by monitoring user behaviour and detecting suspicious activity that may indicate compromised credentials or insider threats. By analysing identity-related signals, the platform helps security teams identify unusual access patterns and respond quickly to potential attacks.
Together, Microsoft’s identity and security solutions form the foundation of a zero-trust security model. In this approach, no user or device is automatically trusted, even if they are inside the corporate network. Every access request must be verified, validated, and monitored continuously.
As organisations continue to adopt cloud services and hybrid working models, identity has become the primary security perimeter. IAM solutions, supported by platforms such as Microsoft Entra ID and Microsoft Defender, allow businesses to secure that perimeter while maintaining seamless access to the tools employees need to perform their roles.
Strategically implemented, Identity and Access Management not only strengthens cyber security but also enables organisations to scale operations, adopt new technologies, and maintain compliance with confidence.
To discuss IAM services and Microsoft Entra deployments, please get in touch:
Contact Us